



 (22 votes, average: 4.09 out of 5)
(22 votes, average: 4.09 out of 5)Over the past few weeks the digital certificate industry, as well as the greater cybersecurity community, have been busy debating adding a new root certificate. In their attempts to find a technical reason to disqualify the new root request, a researcher inadvertently turned up a misconfiguration in the EJBCA CA tool that many other CAs use to generate serial numbers.
According to the Baseline Requirements that govern digital certificate issuance, all certificates must be issued with a serial number that is a unique, positive integer with 64 bits of entropy. As a result of this misconfiguration, certificates were being issued with 63-bit serial numbers, which constitutes a mis-issuance.
That means the certificates have to be revoked. If the website owners don’t replace the revoked certificate with a new certificate, they’ll get an error message like this: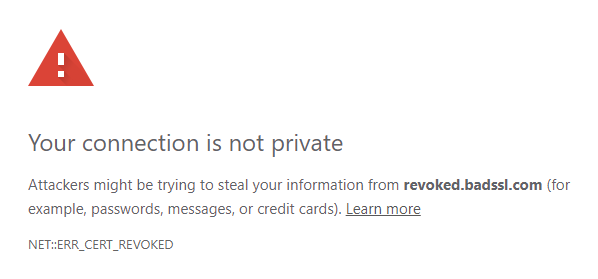
As of now, Apple, Google, GoDaddy and a handful of other CAs have started revoking over 1,000,000 mis-issued digital certificates.
Comodo CA (now Sectigo) is not one of those Certificate Authorities. We would like to clarify that NO active public certificates from Sectigo/Comodo CA are subject to this flaw.
Comodo CA certificates were all issued correctly, and none of them will be revoked. You can continue using your certificates under the Sectigo, Comodo, InstantSSL, EssentialSSL, PositiveSSL, and EnterpriseSSL brands with no change or reissuance required.
Sectigo/Comodo CA has been in business over 20 years securing websites, email, documents, software – you name it. It’s never had a major PKI failure or a mass revocation. In fact, Sectigo is so serious about avoiding mis-issuance and fraud using its certificate that it offers a mechanism for reporting any suspicious certificates.
Get A Comodo SSL Certificate For Your Site
Digital Certificates are important for security, but even more critical for compliance. There are strict standards across a number of industries that require organizations to encrypt and secure their communications, sign documents, encrypt important files/emails, etc.
To accomplish this, you need your digital certificates – especially the publicly trusted ones – to be compliant. You can’t be compliant if your certificates aren’t compliant.
Unfortunately, this week millions of websites and organizations discovered they are suddenly non-compliant as a result of a mistake they had no part in. That not only undermines confidence in the issuing CA, but also in the industry as a whole and in the technology itself. While the actual security risk posed by the 63-bit serial numbers is negligible in light of recent advances in cryptography and the SSL/TLS protocol, the compliance element is what the business world will find most troubling.
This just goes to show that even the best, most compliant organizations can have everything undone by the mistakes of a partner.
As always, if you have any questions or concerns about your Sectigo/Comodo CA products, or if you’d like to switch to a more reliable Certificate Authority – and avoid these kinds of situation in the future – please give us a call. Or chat with one of our experts by clicking the window at the bottom of the screen.