How Do Code Signing Certificates Work?
A closer look at how Code Signing Certificates protect the integrity of your software
Years ago, before the internet was capable of delivering high download speeds – back when laptops still had disc drives – we used to buy our software from brick and mortar stores.
It was a simpler time, back then you knew the software you were purchasing and installing was safe because it had come from a trusted retailer, in shrink-wrap no less, so you could be sure it had never been tampered with.
Nowadays though, we download most of our software directly from the internet and the safeguards and guarantees that came from purchasing it in person, from an actual physical store, are much harder to find. This, in turn, has caused consumers to become much more skeptical. After all, it’s hard to tell if the software or code you think you’re downloading is the legitimate article, or that it’s never been altered.
However, if you’re a programmer or software developer there is still one way to guarantee the integrity of your software/code to your consumers. It’s called Code Signing—and that’s what we’ll be talking about today.
What is Code Signing?
Code Signing, as the name implies, is a way for programmers and developers to literally sign their scripts and executables before publishing them. Signing your software/code essentially serves two functions:
- It provides cryptographic protection against the modification of the code/software
- It identifies the author of the code/software
As you’ll come to see, both of these are absolutely essential if you’re programmer or developer.
We’ll start with protecting against modification—which may be a bit of a misnomer. You see, you can still technically modify signed code. It’s not as if code signing creates a hard barrier against any kind of modification. Code, after all, is malleable. It can be altered.
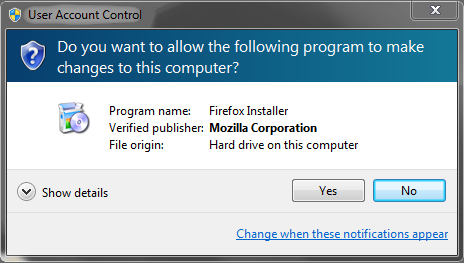
Rather, when a code signing takes place a digital signature is created. The signature tells both who signed the code and what code was actually signed. Meaning any alterations to the code, will cause the signature to change as well. In this case, when the code is executed and the computer running it checks the signature, it will immediately flag as having been tampered with. The computer then notifies the user that the software may be unsafe, thus avoiding any potential problems.
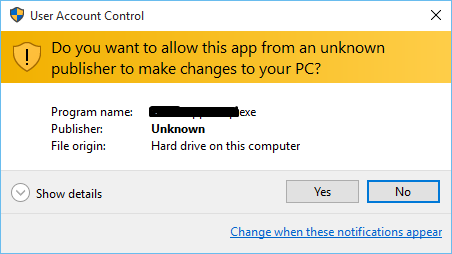
Altering downloadable code or software is a regularly used attack vector for many hackers. But when a code-signed downloadable is altered, the changes are obvious to the computer running it. This has to do with how the signature is hashed. You see, a digital signature is not actually a signature at all, but rather a string of data. When that data is hashed, it gives off a specific value that the tells the computer running it who signed the code, and what code was signed. Any alteration to the code will cause the signature to give off a different value, which immediately notifies the computer running it that something is amiss.
The other aspect of code signing has to do with identity. Much like with SSL Certificates, authentication is important when it comes to distributing software. People want to know who made the code they’re downloading. By allowing you to sign your software, Code Signing is authenticating you as a developer.
This authentication builds trust. There are two kinds of Code Signing Certificates. There are Organizational ones, which authenticate an entire company, and Individual ones, which can authenticate a single programmer. Both require you to prove your identity and legitimacy to the issuing certificate authority.
In turn, when a potential user sees your identity as authenticated by a CA, they know you have passed certain standards and are a trustworthy source.
So to summarize, briefly, Code Signing Certificates protect the integrity of your software by notifying users if the code you have written has been tampered with and no longer comes as you intended it. And, in addition to protecting the code integrity, it authenticates you as an organization or individual programmer, thus inspiring trust from your potential consumers.
So, How Does Code Signing Work?
Code Signing actually works very similarly to SSL in many ways—that’s why many CAs sell both.
We’ll start by looking at the process of obtaining, installing and using one:
- You purchase a certificate. Depending on whether you’re an organization or an individual, you choose the right Code Signing option for you. There are even EV Code Signing Certificates available.
- The CA verifies your identity. The process differs depending on whether you’re a company or an individual, but suffice it to say the CA wants to make sure you are who you say you are and that you’re operating in good faith before they authenticate you.
- You install your Code Signing Certificate. This one is pretty straightforward, you install it on whatever platform you’re using.
- You start signing your executables and scripts. Every platform handles the actual signing process a bit differently, but one thing is the same, this is where you add your digital signature. As we just discussed, the digital signature really isn’t a signature at all, it’s just a string of data that can be hashed to display your identity and whether or not your code has been altered.
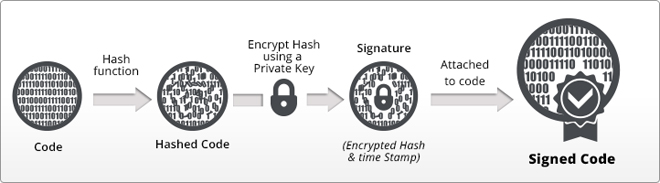
- You distribute your signed software. This is the last step. After you have signed your software/code, you can begin distributing it. Anyone who proceeds to download and run it will be presented with your signature, which, when hashed, will display your identity as a programmer and whether or not the code has been tampered with since you published it.
It’s really as simple as that. Your digital signature contains information on your identity and what exactly it is you signed.
Most of the time it’s suggested you timestamp your digital signature as well. The reason for this is because, like SSL Certificates, Code Signing Certificates come with a validity period. Usually 1-3 years. By timestamping your digital signature, it tells the computer reading that signature that the software was signed during the Code Signing Certificate’s validity period. This allows the signature to remain valid, even if the Code Signing Certificate that signed it no longer is.
Conclusion
There you have it, that’s a fairly cursory explanation of how Code Signing Certificates work. Remember, a Code Signing Certificate allows a programmer or developer to sign their software with a string of data that, when hashed, will display their identity and tell the user whether the code has been altered at all.
It may not seem like much, but in the world of software development or distribution, that little digital signature makes all the difference. It assures customers of the developer’s identity and gives them peace of mind that they’re downloading what the developer intended.
![]()
Why EV Code Signing Certificate
Let’s understand why big and small software publishers need ev code signing certificate for their software security. Read our full guide
Learn About EV Code Signing Certificate



 (13 votes, average: 3.77 out of 5)
(13 votes, average: 3.77 out of 5)