How to Fix the WordPress Redirect Malware Issue on Your Website
A recent SiteCheck report reveals that around 11,000 websites were infected with sneaky malware that redirects visitors to fraudulent ad-viewing sites.
Malware can harm websites in various ways, including through “WordPress hacked redirects” (sometimes called a “WordPress website redirect hack”). Much like the name implies, this occurs when hackers exploit compromised websites to redirect visitors to their dangerous sites, leading to significant consequences for website owners and visitors alike. These attacks often involve the use of WordPress redirect malware.
When confronted with a WordPress website redirect hack, the aftermath can be frustrating and far-reaching. Not only does it disrupt your website’s traffic, causing a sudden drop in organic visitors and a skyrocketing bounce rate, but the most significant damage lies in the erosion of customer trust. The longer you delay addressing a WordPress redirection hack, the greater the damage it can inflict.
Whether you’ve already been hit or want to stay ahead of the game, our step-by-step instructions on how to fix WordPress redirect hacks will be your go-to resource for removing the stubborn redirect malware from your site.
WordPress Redirect Hack Fix: How to Mitigate This Issue in 6 Actionable Steps
Hackers are like sneaky tour guides, taking your WordPress website users on a detour to spam and advertisement sites. They do this without your knowledge or permission. Not only does this increase spam and potentially blocklist your site, but it also confuses and frustrates your visitors.
Don’t let these cyber criminals hijack your website and the organization’s reputation! Take proactive steps and implement these methods to clean and secure your WordPress site, so you can return to being your online ship’s captain.
1. Prioritize Creating a Backup Before Any Action
First things first, it’s ideal to maintain regular backups to ensure the safety and functionality of your WordPress website. It’s like indemnifying your site for an unforeseen event, such as a cyber attack or a WordPress website redirect hack.
Secondly, by creating comprehensive backups, preferably on a separate server, you ensure that even if your site encounters problems during cleanup or security breaches. How? Because you’ll have a working version readily available to restore and get your site back up and running quickly.
Now, if your website is large and receives daily visitors, it’s likely that you already have regular backups in place. In such cases, restoring the most recent backup is typically the best option, even if it means losing some recent updates.
Many hosting providers offer automatic backups through cPanel, or you can utilize backup solutions like CodeGuard to back up your site and simplify the restoration process. These backup mechanisms are invaluable for resolving issues without starting from scratch. Remember: backups serve as a safety net, giving you peace of mind and the ability to recover your site swiftly in the face of adversity.
Learn More About CodeGuard WordPress Backup2. Unmask Sneaky Malware with a Website Scanning Tool
WordPress redirect hacks often occur because many WordPress website owners neglect to install a security scanner, leaving their site vulnerable to malware or malicious code injections that can go undetected for extended periods. If you’re not taking proactive measures, you may not realize something’s wrong until a customer or other user informs you.
Rather than waiting for someone to tell you something’s wrong (i.e., when it’s too late), scan your website for malicious code, and WordPress redirect malware proactively. Even if your site hasn’t been hacked or affected, learning how to scan your WordPress site for malicious code and injection vulnerabilities is essential. This knowledge will help protect your website from future attacks and empower you to enhance your WordPress security, effectively fortifying your site like a pro through appropriate tools.
Learn How to Scan Your Site with SiteLockAlternatively, Google diagnostic also provides detailed information on the number of infected files and directories. So, you can utilize the Google Transparency Report to scan and pinpoint the precise location of the infection to capture malware on your site.
We have discussed purging malicious code using Google Console at length later in the article.
3. Identify and Clean Malicious Redirects
When dealing with suspicious encrypted code on your website, it’s essential to take a systematic approach. While scanning every page for malicious code can be overwhelming, narrow your search for malicious code and focus your efforts on the below-given areas where the code is often found.
Primarily, if you are experiencing redirects, scan these critical areas:
- .htaccess: The cloaked keywords and link hack utilize your .htaccess file to create cloaked pages on your website. Check this core file regularly for unauthorized redirects or other changes.
- index.php and index.html: Check these files for unauthorized modifications, as hackers often replace these files with infected copies in WordPress hacks.
- wp-content: Debug this folder to check for corrupt themes and plugins.
- adminer.php: Keep an eye on this one. As a favorite developer third-party tool for managing database content, it’s often prone to hacking and malicious script injections.
It is often tricky to pinpoint the URL of the website where redirection occurs, so after cleaning, rescan the website for viruses and repeat the process to identify any remaining infected files.
4. Mitigate Disruptive Malware Downloads
To fix a redirect code that causes annoying (and potentially dangerous) downloads, check for unfamiliar code snippets that may indicate the presence of malware in your WordPress website’s theme folder:
- header.php
- footer.php
- functions.php
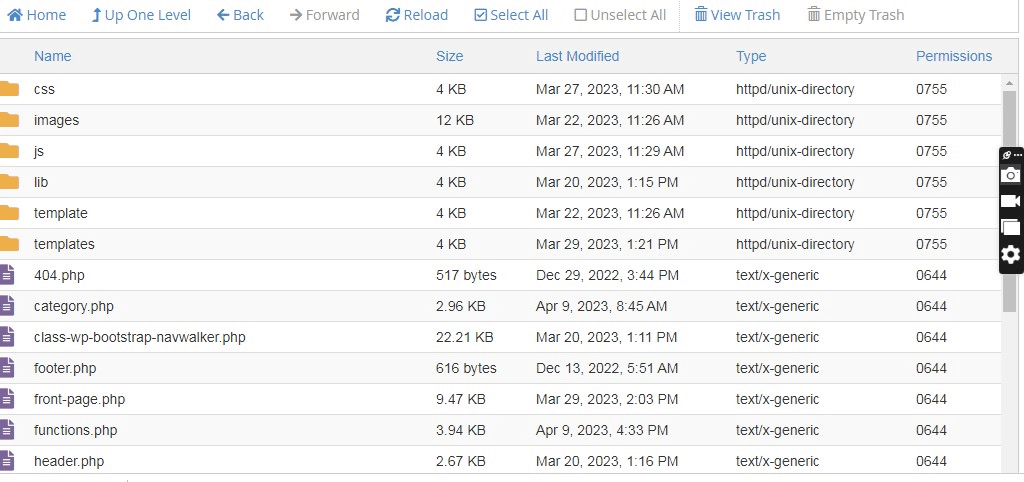
Next, replace any infected themes or plugins with legitimate versions. Simultaneously, be sure to check your index files and wp-content for embedded scripts or pop-up triggers:
- Index files (both .html and .php)
- wp-content/themes
- wp-content/plugins
Replace any suspicious or encrypted files with new versions. Also, as part of the inspection, disable recently installed plugins and re-enable them one by one to check whether they are causing the problem.
If the issue persists or you need further assistance, consider reaching out to a web developer or security professional. They can provide a more thorough investigation and help resolve the problem effectively.
5. Stop Unseen Redirection Scripts
Hackers commonly establish backdoors (for future redirect hacks) within websites, often disguising them with names that resemble legitimate files.
Knowing this, conduct manual searches within your website’s files to identify potential malicious PHP functions, such as eval, base64_decode, gzinflate, preg_replace, str_rot13, and eval.
Nonetheless, it is also important to exercise caution, as legitimate WordPress plugins may use these PHP functions for valid purposes. (Note: You must avoid accidentally damaging your site; for non-coders, seeking professional assistance while performing these checks is better.)
6. Purge Malicious Code from Google
Developers often rely on Google’s expertise to effectively address website malware issues. The search engine has listed third-party browser extensions for identifying and removing malicious content to promote user security.
In December 2022, Safe Browsing flagged 3.5 million unsafe websites, but the number of warnings has significantly decreased over the past decade.
If you identify any harmful code, removing it from Google is a square process. Here’s what you need to do:
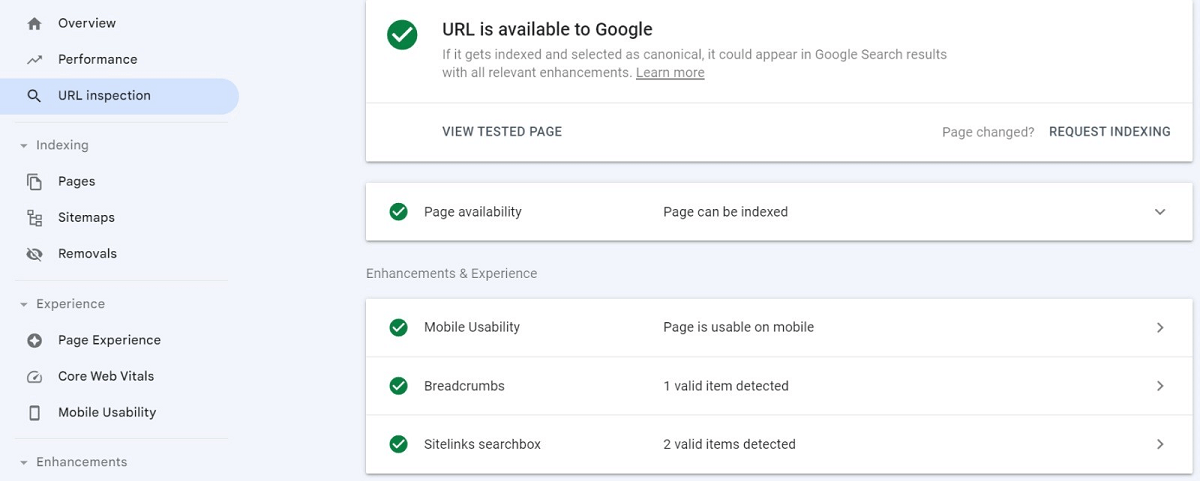
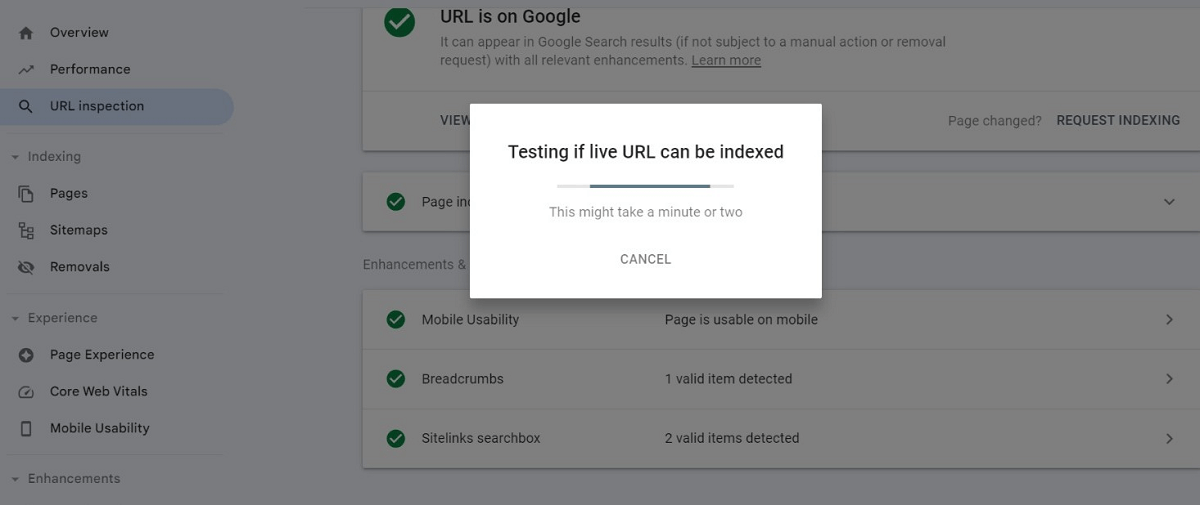
- Begin by accessing your Google Console.
- Inspect your website URL using the URL inspection tool in the toolbar at the top.
- Carefully examine any warning messages and error logs provided.
- Address any identified issues or vulnerabilities.
Reindexing Severely Infected WordPress Site
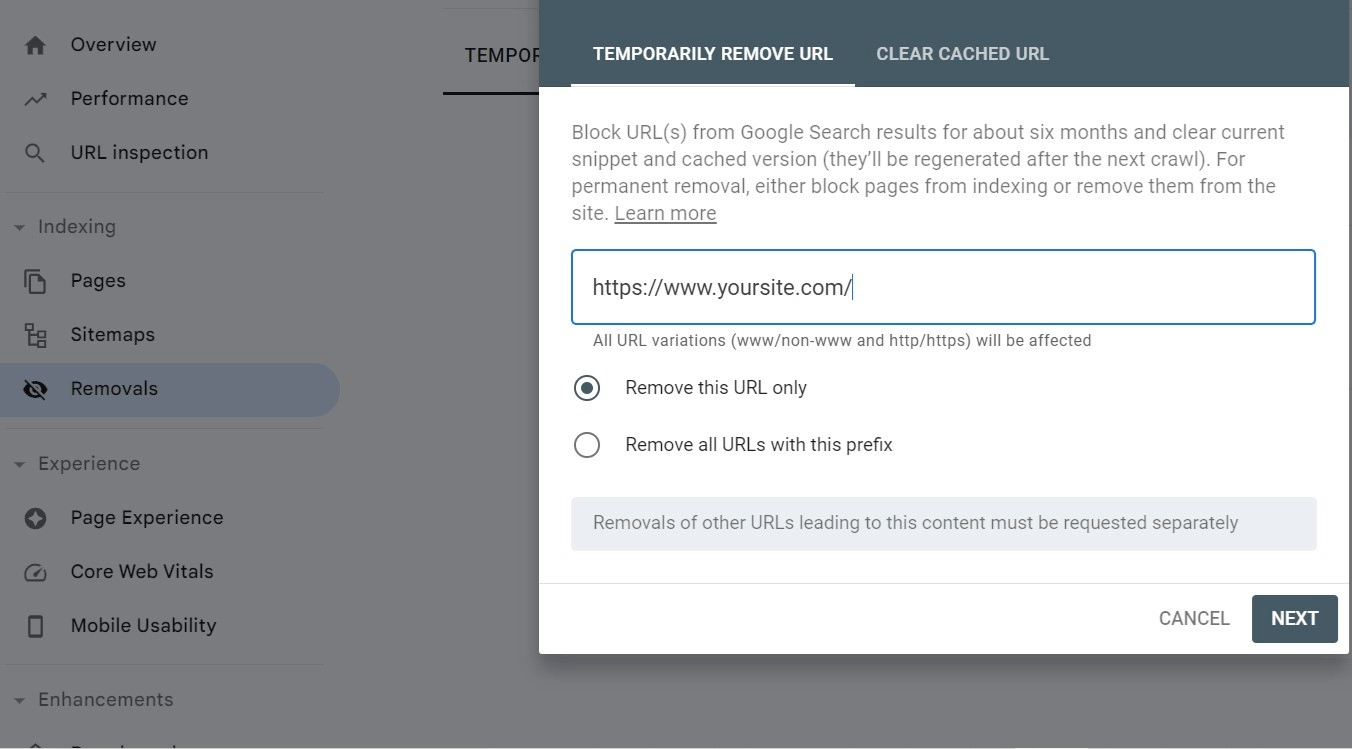
In case your website is severely infected, take the necessary steps to remove it from the Webmaster Tool and request site reindexing.
- To do this, access the Removals section within your Google Webmaster Tool.
- Enter the URL of the infected page or section in the prompt field. Google will remove it quickly from its index.
- After the site cleaning, you can proceed to reindex your website.
Remember to follow the same process for other search engines if you have a Webmaster account with them.
Final Thoughts on Fixing WordPress Redirect Hacks
In conclusion, the above steps systematically cover how to fix the pesky WordPress redirect hack and keep your website secure. But don’t just stop there! Be sure to follow WordPress security best practices, which include strong access controls and keeping your site’s plugins and themes updated.
Also, make sure you’re using the right security plugins and regularly backing up your site to prevent any future attacks.
With these measures in place, you can rest easy knowing your website is safe and sound and that you aren’t experiencing WordPress website redirect hacks.

Stay ahead of hackers, malware and security threats with SiteLock – the #1 rated security solution trusted by over 300,000 sites worldwide.
Prevent WordPress Redirect Hack with SiteLock Security
Don’t let a hacked WordPress site slow you down! If you’re short on time or lack the expertise to scan and clean up the mess, SiteLock is here to save the day.
With the trust of 12+ million website customers, SiteLock leads as the global authority in website security. Our cloud-based WordPress priority service will restore your hacked site in no time — often within 24 hours! With SiteLock, you can:
- Scan and eliminate all malware, replacing infected files with fresh, secure copies.
- Bid farewell to backdoors, blocklist warnings, and common vulnerabilities.
- Gain added protection with the hack recovery feature, WordPress hardening, automatic updates and patches, and secure backups.
Finally, never let a site hack disrupt your online presence — trust SiteLock to keep your WordPress site safe and secure. Contact us today to learn more!