What is Digital Signature? How does it Work?
An in-depth insight into the most modern technique of signing
In a day and age when incidents of data tampering and forgery are growing increasingly prevalent, it has become imperative to protect any data sent online and for that reason, Digital Signatures are growing in popularity amongst professionals thanks to their ability to validate the authenticity of a document, file or software.
![]()
58% Off Comodo Code Signing Certificates
Save up to 58% on Comodo Code Signing Certificates. Works on any platform except Apple.
Compare Comodo Code Signing Certificates
Digital Signature: A Faster, Safer and Cheaper Alternative to Conventional Methods
As the name itself implies, a Digital Signature is a type of signature, but the only difference is that it involves the use of mathematical pin or algorithm to sign and validate the authenticity of a document, file or software instead of pen and paper.
A digital signature is used to make sure that the file(s) sent digitally belongs to a designated source and reaches the intended receiver in its original format without any tampering. In simple terms, a digital signature works in the same way as an envelope seal does.
Imagine wanting to send a physically signed document from one country to another. You would need to send the documents by means of a courier. This process involves loads of paperwork and thereby wasting invaluable time. Instead, if you had just used a digital signature, the documents could have been sent electronically in a matter of minutes. This way you can save time as well as money. Numerous studies conducted around the world show that using digital signatures can save a whole working week for any working professional. The time saved combined with the undeniable savings in money is surely going to fuel the rapid acceptance of digital signatures around the world.
How does a Digital Signature Work?
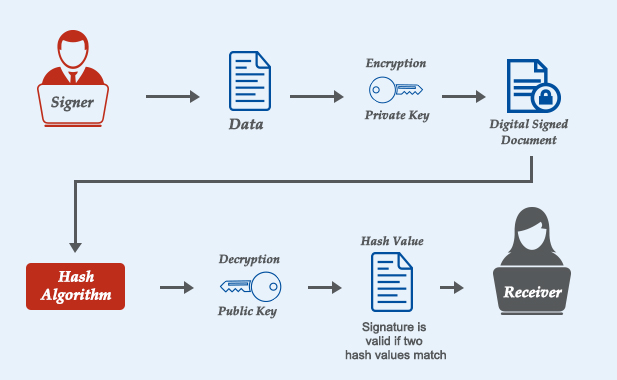
Digital signatures are based on Public Key infrastructure. By this mechanism, two keys are generated, a Public Key and Private Key. The private key is kept by the signer and it should be kept securely. On the other hand, the receiver must have the public key to decrypt the message.
For example, a person named Charlie wants to send an encrypted message to Lisbon. As stated above, Charlie must have a private key to sign the message digitally.
Before encrypting the message using the private key, an algorithm named ‘MD algorithm’ encrypts the message to be sent by Charlie into a 128/256-bit format known as a hash value. Then Charlie’s private key encrypts this hash value. On completion of both the processes, Charlie’s message is said to be digitally signed.
On the side of Lisbon, the digitally signed message is decrypted with the help of the signer’s public key. The public key decrypts the message and converts it into another hash value. Then the program which is used to open the message (e.g., MS Word, Adobe Reader etc.) compares this hash value to the original hash value which was generated on Charlie’s side. If the hash value on Lisbon’s side matches with the hash value generated on Charlie’s side, then the program will allow the message to open up and displays the message “The document has not been modified since this signature was applied.” The program will not allow the document to open if both the hash values don’t match.
Digital Signatures: The Way Forward
The rise in data tampering incidents has caused a significant upward trend as far as the acceptance of digital signatures is concerned. Recent research done by Credence Research Inc. shows the global Digital Signature market is growing at stunning CAGR of 24.2% from 2017 to 2025. Moreover, in many countries, digital signatures are equivalent to handwritten signatures. For example, the US government authenticates the digital versions of documents by means of digital signatures.
Bearing in mind the benefits involved along with the potential dangers, it is safe to say that the digital signature is the way forward.
![]()
Why EV Code Signing Certificate
Let’s understand why big and small software publishers need ev code signing certificate for their software security. Read our full guide
Learn About EV Code Signing Certificate


