What is the Best Way to Stay Safe from Phishing?
Best Practices to Avoid Getting Hooked by Phishing Scams
With every day that passes, it’s starting to become more and more apparent that the Internet is becoming an essential part of our daily lives, but also a frontier for attacks to happen. While a hefty majority of the Internet is positive and beneficial, there’s a negative and harmful portion that is targeting the new online frontier.
Criminals are changing up their tactics and shifting from real world to the virtual world due to the ease of access and wide usage. While their objectives haven’t changed, the tactics and ways to obtain personal details have evolved to a whole new level that is beginning to disrupt Universities, Banks, and Online Retailers. These criminals are sending out millions of Emails, Tweets, and Facebook messages to attempt to lure people into believing that they’re someone they’re not to obtain their personal information.
What is Phishing?
Phishing is a fraudulent activity that is typically carried out online by criminals in order to steal user’s confidential information such as their credit card details, site passwords, and social security numbers. While phishing is defined as an illegal activity under the ‘IT Act’, there’s been very little action taken against the criminals until its already impacted thousands. The reason why little action has been taken is because of the methods used, phishing is performed over a wide spectrum from a fake e-mail, all the way to fake letters to your home.
Even though phishing is still relatively new and on the rise as more users get connected, attacks that are carried out through email have actually been starting to die down due to education of these attacks. That’s still not going to prevent criminals however, they’ve now shifted to alternative methods like social media to lure users with what some call ‘link bait’ (juicy article titles that sound too good to be true). While clicking a link might not seem like a big deal, the actions that are then carried out while loading the page could leave with a malicious software or tool in your computer.
How to Prevent from Phishing Scams?
Phishing attacks are becoming a more and more serious threat due to them targeting millions of users. Sadly, since phishing attacks first arrived there’s been no decline in growth, but instead a rapid growth.
While we’re not capable of preventing you from being a target, we’re more than capable of providing some knowledge that can prevent you from falling a victim!

Two-Factor Authentication
Two factor authentication (also called as 2FA) delivers unmistakable identification of user with two different components to validate the identity of the user. These two components typically consist of a physical token like a card or a key and the other is some recognized secret security code such as username, password, PIN, TAN etc. It’s these random security codes that make Two-Factor authentication one of the best & most secure techniques available as the hacker can’t access your account until they know the randomly generated security code that you will receive. The days of having just email and password are sun setting away, and won’t be secure enough to protect you much longer.
Be Aware of a Suspicious Email
Every day, millions of junk emails are sent by scammers for the sole purposes of phishing your information. These emails mock the design and wording from an actual site, but the actual links contained within the email often lead to somewhere quite malicious. If you’re ever unsure about the email that was sent to you, you should delete the email immediately. Such examples that may lead you to doubting the authenticity of the email is see any spelling mistakes, or if it lacks any identifiable information,
Website Security & Trust
As we talked about earlier, criminals are using a wide variety of methods to attempt to phish user’s information. An example of a rising concern is building a similar website using the same layout, text, and even logo to make it look like the actual website. The only issue is that when a user attempts to login, his/her account details are now phished ready to be used and abused by the criminal.
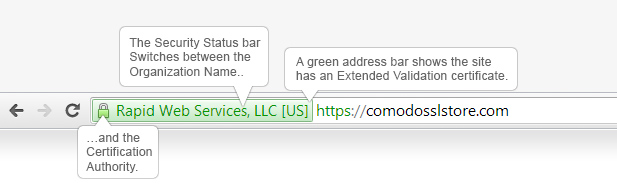
Before proceeding with any confidential information such as a Credit Card or Login, make sure you’re accessing the website over a secure connection ‘HTTPS://’ instead of an insecure connection ‘HTTP://’.
Note: For most high profile websites such as PayPal, they’ll have a ‘green address bar’ that will assure you’re on the right website.
Keep Your Browser & Computer Up-To-Date
By receiving regular updates for both your web browser and computer can help prevent certain exploits from being used on you. The days of just keeping your browser up-to-date is not enough anymore; you’ll also want to update both your applications and operating system periodically (bi-weekly is suggested). Most operating systems and applications will have an automatic update mode that will check for the latest patches and fixes, and if they’re available it’ll install them for you.


