What is A Root CA Certificate and How Do I Download It?
A Root CA certificate is at the heart of the reasons why SSL certificates are trusted, so knowing how they work can be useful
Every root CA certificate is the reason that SSL certificates are regarded as the standard basis for website security today. Considering cybercrime damages are projected to reach $6 trillion annually by 2021, keeping your business’s cyber security measures in check should be at the top of your priority list.
One such measure that constitutes a meaningful part of your business’s cyber security are SSL certificates. SSL certificates essentially serve as a “watchman” for your company website, encrypting all data that is sent or received by the site (e.g. passwords, customer information, etc.) while it’s in transit.
Why are SSL certificates important? Well, in short, they keep your customers’ data secure and make being compliant with industry standards like the European Union’s General Data Protection Regulation (GDPR) easier to reach.
This article isn’t focus on SSL certificates themselves. Rather, our focus is on the trust system foundation upon which they work — their root certificates.
![]()
Save Up To 80% When You Buy SSL Certificates Direct
Tip: you can get the lowest price on SSL certificates when you buy direct instead of through your hosting company.
Buy SSL Certificates
Save Up to 75% On
Comodo SSL Certificates
Tip: You can typically save a significant amount by buying your SSL certificate direct instead of through your web hosting company. We sell all Comodo SSL certificates at up to 75% off.
Root CA Certificates and the Certificate Chain
SSL certificates operate on a structure called the certificate chain — a network of certificates starting back at the issuing company of the certificate, also known as a certificate authority (CA). These certificates consist of root certificates, intermediate certificates, and leaf (server) certificates.
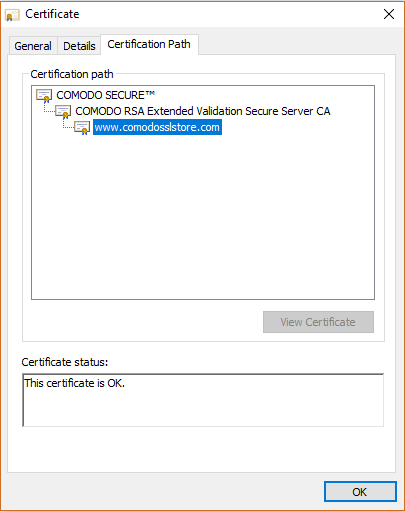
The SSL certificates that consumers buy at places like ComodoSSLStore are simply the tail of the certificate chain. There’s a whole other animal that completes the chain: Intermediate and Root certificates.
Intermediate certificates are certificates that are designed to mitigate risk by creating a separator between the root certificates and SSL certificates. This is because issuing a certificate straight from the root would be too dangerous if it were to become compromised, as the root certificate has the most authority and needs to be protected.
There’s one main reason Intermediate certificates exist: creating a barrier to entry. For example, if a server SSL certificate were to get compromised in a way that allows access to the intermediate certificate, the root is still safe, as it didn’t directly issue the SSL certificate.
As for Root CA certificates, these are certificates that are self-signed by their respective CA (as they have the authority to do so). Every valid SSL certificate is under a Root CA certificate, as these are trusted parties (like Comodo or Sectigo) who have been established in the industry as security leaders.
How Do I Download My Root CA Certificate?
Typically, you don’t need to download a Root CA certificate, as they are included in web browsers’ trust stores and are even pre-installed on some operating systems. This allows your computer to be able to tell whether or not a certificate is invalid, because if its root certificate isn’t on their trusted root CA list, then it’ll warn you that the certificate is not a trusted one.
These trusted root lists are also updated as new CA’s emerge, so there’s no need to worry about your certificate not being trusted if it came from a relatively new CA. However, if you do need to download your Root CA certificate for whatever reason (such as starting your own CA or self-signing), you can download the necessary certificates on Comodo’s Support Page.
![]()
Save Up to 85% on SSL Certificates
Get SSL certificates that authenticate your identity and secure your site with prices that start as low as $7.27 per year!
Shop Now

 (18 votes, average: 4.11)
(18 votes, average: 4.11)