Rate this article: 



 (1 votes, average: 5.00)
(1 votes, average: 5.00)




 (1 votes, average: 5.00)
(1 votes, average: 5.00)SSL/TLS certificates are essential to web security. They became mandatory in 2018. But misconfiguring one can cause a whole load of unintended problems.
For instance, the NET::ERR_SSL_PINNED_KEY_NOT_IN_CERT_CHAIN error (sometimes written as NET ERR_SSL_PINNED_KEY_NOT_IN_CERT_CHAIN or ERR_SSL_PINNED_KEY_NOT_IN_CERT_CHAIN). That’s Google Chrome’s nomenclature for a server-side error — the same error also appears as MOZILLA_PKIX_ERROR_KEY_PINNING_FAILURE in the Mozilla Firefox browser.
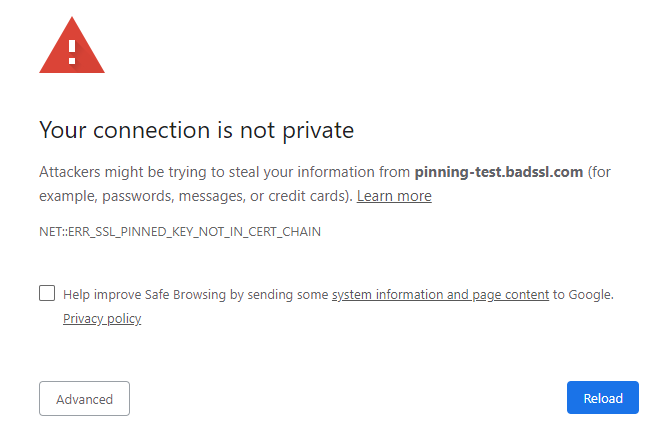
Terminology aside, the cause is the same either way. And we have good news and bad news. The good news is that if your website is having this problem, we can help you fix it. The bad news is that if you’re just trying to visit the website and your browser is issuing this error — or to put it another way, you are just a web user, not a site owner — you’re totally out of luck.
As we just said, there’s no way to fix this issue if you don’t own the website. The best you can do is contact the site owner and wait for the issue to be fixed. Don’t click through the warning or connect via HTTP as this exposes you to undue risk.
This is a key pinning error. HTTP public key pinning (HPKP) was a great idea, in theory, but it’s prohibitively difficult for all but the most sophisticated and technically mature organizations. Regular website owners should not attempt it.
Chances are, someone suggested you attempt key pinning, which didn’t go as planned. The error itself is communicating that one of the keys you have pinned isn’t bound to the certificate you pinned it to. These keys are not interchangeable; failing to pin the right keys to the correct certificates can break your entire site… As it just did.
And it’s not just your own keys you need to pin; you also need to pin the keys for the rest of your certificate chain — save the root, whose key is included in the root stores. Keep in mind that when a visitor arrives at your website, the server hosting your site presents the user’s browser with the certificate. The browser uses those public keys to verify the signature on each certificate and trace it back to the certificate that left it.
Even if you pinned your own certificate’s key correctly, mis-pinning any other intermediate public keys can still cause this problem
The fix is simple:
STOP PINNING YOUR KEYS!
It’s like the old joke about the guy who says to his doctor, “it hurts when I do this.” To which his doctor responds, “well don’t do that, then.” This situation is the same scenario. Experts advise against key pinning. We advise against key pinning. This is one time it doesn’t pay to be subversive.
Simply re-install your certificate and any intermediates in the standard way. This may require you to remove the previous configuration, but that shouldn’t take longer than a minute or two. Just follow the STANDARD instructions and your site should work just fine.
Just stop pinning those keys.

You can typically save a significant amount by buying your SSL certificate direct instead of through your web hosting company. We sell all Comodo SSL certificates at up to 75% off.
Purchase Comodo SSL Certificates