Rate this article: 



 (56 votes, average: 2.89)
(56 votes, average: 2.89)




 (56 votes, average: 2.89)
(56 votes, average: 2.89)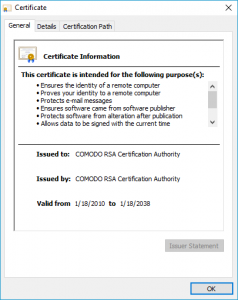 Comodo RSA Certification Authority refers to one of the Comodo CA (aka Sectigo) root certificates. This is actually Comodo’s issuing root, meaning that other SSL certificates are signed by it and chained to it.
Comodo RSA Certification Authority refers to one of the Comodo CA (aka Sectigo) root certificates. This is actually Comodo’s issuing root, meaning that other SSL certificates are signed by it and chained to it.
With over 100 million websites secured, Comodo is one of the most trusted certificate authorities in the world. Secure your website with an SSL certificate from Comodo:
A Root or Root Certificate is an issuing SSL certificate that comes pre-installed in your browser’s trust store. Comodo RSA Certification Authority root is one of those trusted roots. In order for an SSL certificate to be trusted a user’s browser needs to work its way up the chain of trust to ensure that it’s chained to a trusted root. If the SSL certificate doesn’t chain to a root directly or through intermediate certificates, it’s not trusted.
The certificate chain refers to the series of connected certificates that lead back to a trusted root. Every SSL certificate must chain back to a root to be trusted. If it doesn’t, the browser will issue a warning to its user. That’s usually enough to dissuade them from visiting. And they may not come back.
A trusted root, like the Comodo RSA Certification Authority root, is beyond valuable. So, most Certificate Authorities don’t issue directly from them. A compromised root would be catastrophic and could get you untrusted. As a result, most CAs issue intermediaries, these can be used for two purposes:
The CA itself can issue from it, as many do. It can be sold to a Certificate Authority that doesn’t have a trusted root.
When a CA doesn’t have a root and uses another CA’s intermediary, this is called cross-signing.
Click here if you need to download the Comodo RSA Certificate Authority root.